Jeremy Thomerson's Blog
-
Wicket in Action Book Signing
Nov 18, 2008
Martijn signs my book! Yes, it’s dumb, but I took advantage of ApacheCon 2008 by having Martijn Dashorst sign my personal copy of Wicket in Action. Fortunately Bruno Borges was on-hand to document the momentous occasion! Now I just need to meet Eelco……
-
Wicket QuickStart Tutorial
Nov 17, 2008
So, you posted something to the Wicket mailing list saying that you thought you found a bug or you had a problem and were told to “create a quickstart” duplicating the problem. And then you said “how”? There are two ways and each will be described here:
-
Meet the Wicket Community - Little ol' Me!
Nov 12, 2008
After a great week at ApacheCon last week, it was an extra privilege to spend the time with Martijn Dashorst and Bruno Borges. An added privilege was the opportunity to complete my interview with Martijn in person at ApacheCon. To read more about me and my Wicket experiences, check out his interview with me at: http://wicketinaction.com/2008/11/meet-the-wicket-community-jeremy-thomerson/
-
Presented by Bill Au, of the Platform Infrastructure group at CNET
Bill is going to help us learn about how to troubleshoot and monitor java apps, thread and heap dumps, hung or slow apps, OutOfMemoryErrors, and JVM crashes. All of the tools he is going to show us are free tools - open source or free for download.
NOTE: This was a very interesting session. One of the things I was impressed with was his demonstrations of some tools that I have not seen. There was the HP JMeter tool, an open source tool called Samurai, and a perl script that he wrote. All of them look very helpful, and I want to try them all out (not that I have every written any apps that ever have performance issues - but I’m sure I can help someone else look at theirs!)
-
Presented by Ravi Saraswathiamma, architect with AOL / Time-Warner
When setting up an application, you have to identify hardware / software / networking / infrastructure architecture. How do you do this? The first step is of course gathering the requirements - what is required? What kind of application is it? Do you need HTTPS, etc. What are the best practices?
-
Presented by Mark Thomas, committer on Tomcat for five years
There have generally been few Tomcat threats in the wild (at least that have been reported). One in July 2008 was reported that was hackers installing a webapp, always named
fex*.war(*for something - anything). It allowed hackers to get access to a shell on your server. If you were running as root, game over. The way this was being installed was through deployed servers with a Tomcat admin that had not been secured (blank or default passwords). This is obviously a very poor idea.How can you protect yourself against Tomcat security attacks? Read more to find out.
-
Wicket - the power of nested models
Nov 6, 2008
Many times on the Wicket user list, we hear questions like “How do I return a different value when my model object is null?”, or “how do I make a label that says ‘none’ when the model object is null?”, or “How do I make a Label that capitalizes all it’s text?”…. You get the idea. Typically, the gut reaction is to do something like override getConverter in the Label or onComponentTagBody and sort of abuse that facility to change what value the Label uses. This works, but it isn’t reusable. One of the greatest powers of Wicket is creating reusable pieces of code that can be used anywhere in your application.
A great way to create a reusable piece of code to cover this scenario is to use nested models. If you are familiar with Wicket, you know that models, or implementations of IModel, are basically data locators - an abstraction layer that the component uses to locate it’s data. One power that this layer of abstraction gives you is that a component doesn’t need to know where it’s data came from. And, one model can use another model and add on to it’s behavior by composition. Let’s look at some code for a couple of examples.
-
Great new tutorial on Wicket
Nov 6, 2008
Someone sent this to the wicket users list today. There is a great article on IBM DeveloperWorks detailing how to get started with Wicket. It covers a wide array of topics, and if you are thinking of getting started with Wicket (and haven’t yet bought Wicket in Action!), you should definitely check out this article: https://www.ibm.com/developerworks/library/wa-aj-wicket/ Since I’m busy at ApacheCon, I have not been able to read the entire thing.
-
ApacheCon - ModSecurity
Nov 6, 2008
Presented by Ivan Ristic, a web application firewall expert and author of ModSecurity and Apache Security
The problem: HTTP and browsers are designed for document exchange. We have web applications built using a number of loosely integrated technologies. These are created without a lot of thought about security. Things now are better than ten years ago, but there are also more threats now to defend against.
The solution: (or at least one solution) - a web application firewall.
I apologize in advance - Ivan was moving very fast, and many of the notes are sparse as he was jumping from slide to slide. I couldn’t keep up.
-
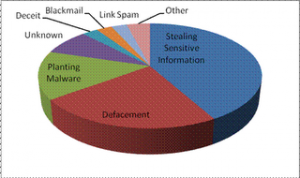
2007 Web Hacking Incident Graph
The Threat Model
Who gets attacked? Everyone! Just because you’re small doesn’t matter. What are the goals of those trying to attack? The chart on the right shows a breakdown based on data from the Web Hacking Incidents Database.
Maybe not so surprisingly was the next slide, that showed that most successful attacks (I think somewhere near 50%) were because of someone getting the admins passwords through some means, perhaps social engineering or phishing. Sysadmins should definitely be more careful with this sensitive data.
So, how do you protect against these attacks? That’s what Sander will cover in this session.